A Beginner’s Guide to Capture the Flag Tools
A week ago, a friend asked me about Capture the Flag (CTF) competitions. I wrote an article about how they’re run — you can read Part 1 here. Today, I want to talk about the tools used and how they help.
Infrastructure
Different CTFs have different environments and requirements. With Trend Micro, they gave us access to their XDR, so only the login credentials were needed. However, that’s not always the case. SANS and FDCA, for example, are website-based: you log in to a portal, each challenge has its own page with files attached, and you submit the flag through a form.
To analyse, you’ll need all sorts of software, and using Windows would be very tedious, so you’ll most likely end up using Kali Linux. It’s a Linux distribution designed for digital forensics and penetration testing. I’ve used it in the most recent SANS and FDCA CTFs. I know Kali is also available in the Windows App Store, so it can be run via WSL. However, since I’m a purist, to me Linux and Windows should never be mixed.
Software & Tools
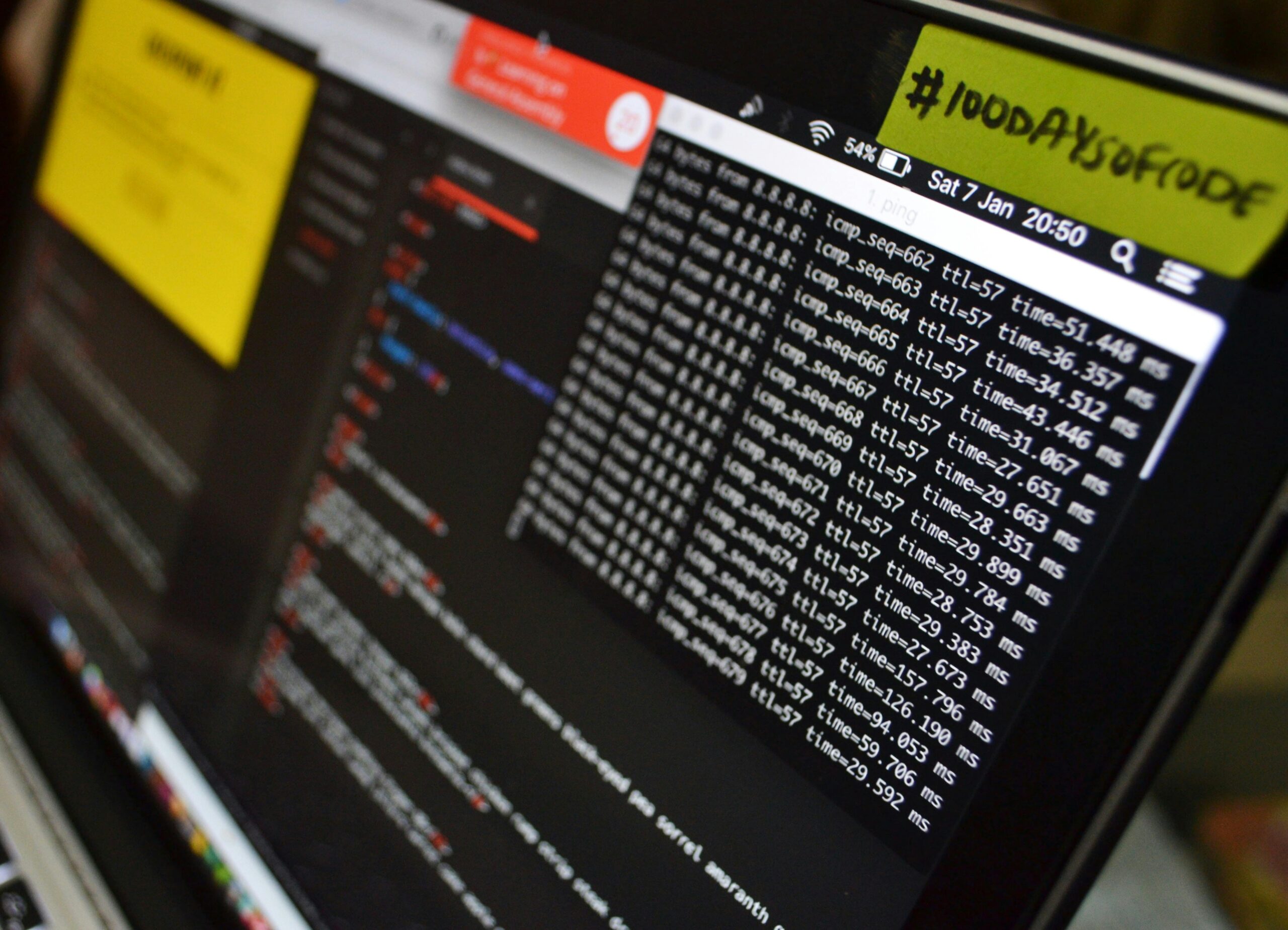
If you want to see a selection of tools Kali provides, here’s a link. From my perspective, I’ve mostly used Wireshark to analyse packet captures and find flags buried in the traffic, Nmap to scan servers for open ports and running services, Burp Suite to probe web applications and watch the requests and responses, and Ghidra to reverse-engineer executables and figure out what they’re hiding. I’m sure I also used some terminal utilities to analyse the files themselves and probe their metadata for clues.
Outside the Kali sphere, I also used CyberChef, which was made by GCHQ. It’s the Swiss Army knife of the digital world. For crypto challenges, for example, you can quickly paste in encoded text and decode it — if you know which recipes to apply.
Recipes in CyberChef are grouped by category — for example, Forensics, Encryption / Encoding, and Extractors. The most popular ones are available under Favourites. If you don’t know which recipe to use, there’s a Magic operation that helps detect the best recipe to apply, so you can make sense of the data.
Finally, a word on AI. It’s now part of how I work through CTFs, and I think it should be for anyone still learning the craft.
The way I’ve used AI in CTFs is this: first I read the challenge description, then I paste it into an LLM and ask for some leads to explore. Some turn out to be dead ends, but what I like about AI is that it brings structure to the challenge. The clock is ticking, and wasting time on the wrong path isn’t worth it.
That wraps up the tooling and systems I use to compete in CTFs. I’ve decided to write a third part next week covering preparation and practice — how to get ready before an event, and where to practice in between.
